The world’s critical infrastructure systems, from water to banking to road networks, operate with the assistance of automated or remote-operational technologies. But in the past two decades, malicious attacks against these systems have increased.
This article was originally published in the February 2025 issue of create with the headline “Critical risk”.
At the turn of the millennium, a disgruntled employee hacked the sewage control system of Maroochy Shire, on Queensland’s Sunshine Coast. As a result, one million litres of untreated sewage was released into local parks and rivers. This caused marine life to perish and creek water to turn black, according to the Australian Environmental Protection Agency, and the stench became “unbearable” for residents.

Since then, cyber attacks against critical infrastructure and operational technology (OT) globally have grown in number, sophistication and severity, and have been carried out by nation states, hacktivists and criminal groups motivated by ideology or money. The Pentagon refers to cyberspace as the “fifth domain”, which adds to the existing domains of land, sea, air and space.
“The fifth domain of warfare is being used in conjunction with other domains of warfare, and what this means for engineers and asset operators of critical infrastructure is that they are now finding themselves on the frontlines of emerging conflicts,” said Bruce Large CPEng, Founder and Principal Cyber Security Architect at B Large, and Chair of the Queensland Branch of the Engineers Australia Information, Telecommunications and Electronics Engineering College.
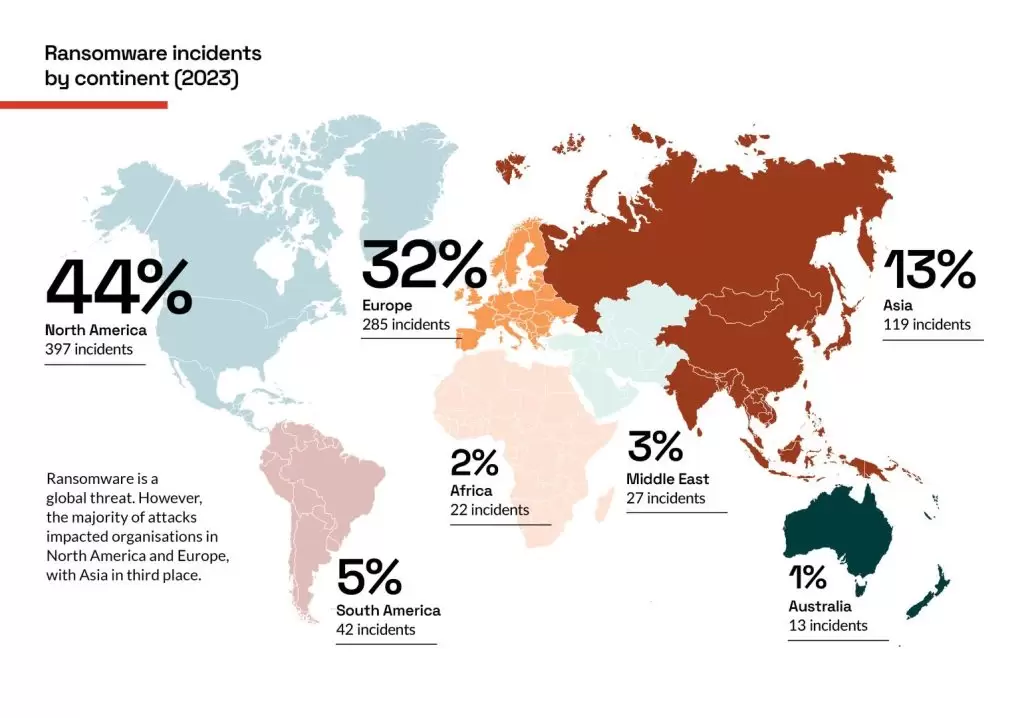
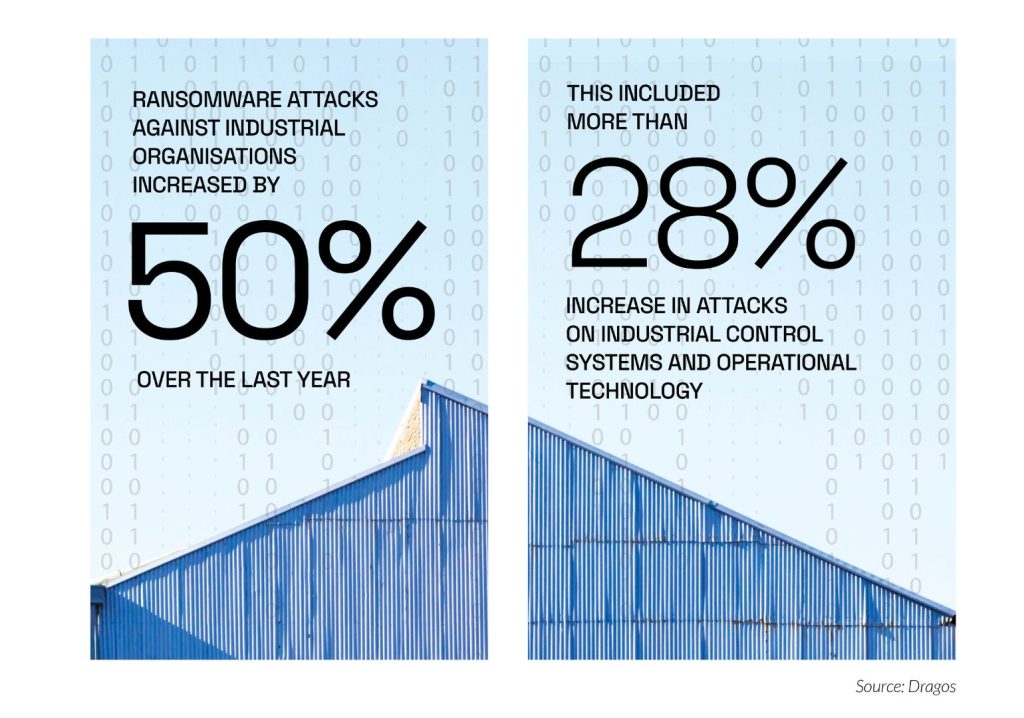
For the foreseeable future, the number one threat is likely to be ransomware. Last year, industrial cybersecurity company Dragos reported 905 global ransomware incidents, with 13 involving Australian organisations.

“It still is the most impactful threat we see to operational technology (OT) environments,” said Hayley Turner, Area Vice President, APAC at Dragos.
“This rise in ransomware attacks is because of the changes we’re seeing not just in the threat landscape, but also in terms of the hyper connectivity and the resulting expansion of the attack surface,” she said. “Many operators lack visibility over their OT environment to have the confidence in its segmentation. In the event of a ransomware incident, the entire OT environment needs to be shut down as a precautionary measure to reduce the risk of it spreading or causing unsafe shutdowns.”
Dragos sees hacktivists as a real and legitimate threat, especially with increasing geopolitical tensions in Europe and the Middle East.
“A lot of ideologically motivated threat groups aren’t necessarily criminals out to make money, and they’re not necessarily state-sponsored, but they’re looking to make their impact well known and highly publicised,” Turner said. “Often, they’ll start targeting critical infrastructure or the revenue-generating assets of organisations they’re trying to go after, because it does have such an impact, and it does generate a lot of noise. We’re seeing their capabilities being far more advanced than what we have seen in the past.”
Organisations often base their security systems around the controls laid out by the SANS Institute. After an analysis of all known industrial control system cyber attacks, SANS created a framework with five elements: OT specific incident response plan, defensible architecture, continuous monitoring, secure remote access and vulnerability management.
“If you can get the basics across those five right, then you’re going to be in a really strong position,” Turner said.
Cyber attacks often can be overwhelming for security teams to handle, and attention is turning to autonomous systems.

“Your day-to-day analysts who work in cybersecurity are simply going to be overwhelmed by the speed and volume of attacks,” said Anna Knack, Lead Researcher, Centre for Emerging Technology and Security (CETAS) at the Alan Turing Institute in London. “There may also be a case where the cyber attacks of the future become too sophisticated and stealthy for humans alone to tackle without the help of autonomous agents.”
However, despite the rapid advances of AI, the technology is not yet at the stage to provide cyber-defence capability. Speaking at a recent IoT Security Conference, Knack presented the results of a Turing Institute survey.
“In future autonomous cyber-defence systems, you could imagine some kind of human machine teaming governance structure where humans act as choreographers or trainers or auditors for the work of autonomous agents,” Knack said. “Humans will still oversee the work that the autonomous agents are doing, the decisions they’re making and the actions that they’re taking.”
Read more: In the age of digital warfare, is Australia’s cybersecurity ready?
Critical infrastructure
Even as cybersecurity technology develops rapidly, business practices and policies are not evolving fast enough.
“Even if reinforced learning and large language models-based systems are able to carry out impressive and sophisticated tasks, we aren’t able to incorporate them into real-world systems, because the policy and infrastructure still needs to catch up,” Knack said.
The Australian Government has drawn up the Security of Critical Infrastructure Act 2018 (SOCI) which outlines the legal obligations for those who own, operate or have direct interests in critical infrastructure assets.

“SOCI puts engineers on notice to ensure our operational technology solutions are up to scratch,” Sean Murdoch, Head of Advisory at Secolve, told create. “The government has identified critical infrastructure aligned to Australia’s national interests, and said, ‘We want to know if you have any incidents, and we want you to manage your risk’.
“For cybersecurity, they guide critical infrastructure providers in good practices to mitigate risk, but leave it up to them to decide the detailed actions and the investments they will take.
“When contrasted with other approaches across the world, the innovation here is the method that the government is using to help critical infrastructure as a body in Australia to uplift their cybersecurity. It’s not sexy tech or a novel tool, but it is pioneering.”
The government is currently undertaking audits to test industry compliance with the SOCI Act. Engineers Australia is calling for further reform to the Act, as the definition of “critical assets” is quite broad and not all included sectors can realistically be considered critical. In some instances, data security needs to go beyond “critical” to “essential”.
Smaller entities managing services and data that enable the delivery of those “essential” services increasingly rely on data to do so.
Engineers Australia also suggests aligning SOCI’s wording to international standard IEC 62443, which was developed to secure industrial automation and control systems throughout their lifecycle. Another recommendation is for Australia to adopt ETSI EN 303 645, which is the European Standard for cybersecurity for consumer internet of things.

“For engineers, an awareness of the threat landscape is a place to start,” said Lesley Carhart, Technical Director, Industrial Incident Response based in Dragos’ Chicago office. “Criminals, hostile states and insiders are using computers to conduct espionage and sabotage on industrial devices. Many cases fly under the radar for long periods of time because when they cause process disruptions, devices are simply swapped out as is standard for maintenance, and no cybersecurity investigation is performed.
“These types of sources need to be considered by vendors and process engineers as part of standard root cause analysis of abnormal events.”
Read more: How does Sydney Metro manage cybersecurity?
Averting disaster
Increasing the awareness of cyber threats could be aided by a home-grown solution. Secolve, an Australian OT cybersecurity specialist business, has developed a video-based OT security awareness platform called OT-SAT to train engineers and critical workers at scale. It also assists continuous improvement organisations to meet regulatory obligations such as those imposed by SOCI and the Australian Energy Sector Cyber Security Framework.
Cybersecurity awareness across a critical infrastructure organisation is an important risk mitigation measure. Traditionally, this has concentrated on the behaviour of individuals in their use of IT in day-to-day activities, such as combating phishing, protecting passwords and caring for sensitive information. With the increased emphasis on OT security in part driven by the SOCI Act, OT-SAT extends an organisation’s awareness efforts into the OT realm.
Protecting infrastructure against cyber attacks is a key area for Knack, who focuses on the European wind power network. In February 2022, a cyber attack on the Viasat satellite network impacted a major German energy company which lost remote monitoring access to more than 5800 wind turbines.
“When something like ransomware attacks happen, the companies themselves will shut down the wind turbines, which could lead to excessive downtime,” Knack said. “If you have a wind turbine on land, you can drive there, but if there’s a cyber attack on an offshore wind farm, there’s a whole process. It can take time to file a report, organise the right team and get a boat to the affected wind turbine. We’re seeing recovery taking months rather than, ideally, hours.
“There is a critical opportunity, before we build this infrastructure more broadly, to start thinking about cyber resilience. Our energy infrastructure, such as wind platforms, will be in operation for decades. If we wait, those facilities are going to stay vulnerable for a very long time. If we want to act on this, now is the time.”
In this EA OnDemand webinar, a cyber defence expert outlines how to strengthen cybersecurity practices in engineering.